Blog Date: December 8th 2022.
Out in the field, I have had a Photon OS appliance like Site Recovery Manager, and vRealize Lifecycle Manager deploy without the proper networking configuration. For me, these appliances have been deployed to a network where the Gateway and DNS were reachable, but the appliance will sometimes complete its first boot without successfully configuring the network. Sometimes you can get out of this situation by simply redeploying the appliance. There are those other times where the appliance just refuses to configure the networking, so a manual approach is required.
DISCLAIMER: I have only done this process on VMware Photon OS based appliances that did not successfully complete their first boot. Your mileage may vary attempting this on an appliance that has successfully deployed.
As always – Take snapshots before proceeding.
Commands To Update Photon OS Network Configuration
Using the VMware console, we first need to check and see what interface is being used with this command:
# /opt/vmware/share/vami/vami_interfaces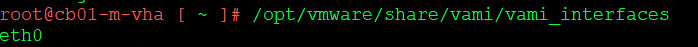
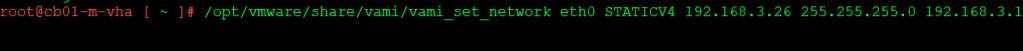
Next we need to set the interface IP, NETMASK, and GATEWAY with this command:
# /opt/vmware/share/vami/vami_set_network <INTERFACE> STATICV4 <IP_ADDRESS> <NETMASK> <GATEWAY>
To set the domain suffix and DNS, use this command:
# /opt/vmware/share/vami/vami_set_dns -d <domain suffix> <DNS1> <DNS2>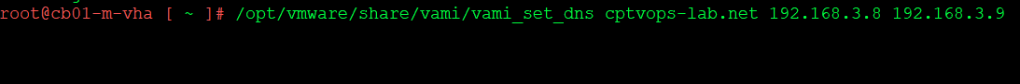
Assuming no errors, reboot the appliance.
In the event those commands do not work because not all Photon Operating Systems are 100% alike, you can also try this method below:
Update Photon OS Network Configuration File:
Let’s first list the network configuration files. To do this, run the following command:
# ls /etc/systemd/network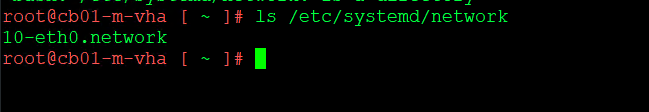
In this example, we see one configuration file “10-eth0.network”. We will use the next command to edit the file using vi and make the appropriate changes:
# vi /etc/systemd/network/10-eth0.network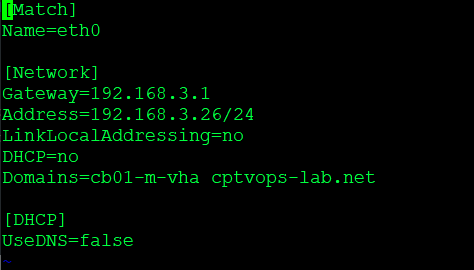
Once you are done making the necessary changes, do a “wq!” to save the changes and quit the editor.
Reboot the appliance for the changes to take affect.

You must be logged in to post a comment.